What makes some industrial components more vulnerable to counterfeit substitution
In global trade and heavy industry, counterfeit industrial components pose serious risks to manufacturing integrity, supply chain resilience, and operational safety. From mining industry news to energy industry news and steel industry news, recurring incidents highlight vulnerabilities in industrial supply—especially for high-value machinery parts, industrial equipment, and processing equipment. Procurement professionals and enterprise decision-makers face mounting pressure to verify authenticity across heavy equipment manufacturing, industrial wastewater treatment systems, and heavy machinery supply chains. This article examines why certain industrial components—such as those used in manufacturing machinery and industrial machinery—are disproportionately targeted, and how equipment suppliers and stakeholders can strengthen due diligence amid rising threats to the industrial industry news landscape.
Why Are Certain Industrial Components More Frequently Counterfeited?
Counterfeit substitution isn’t random—it follows predictable patterns rooted in component economics, technical complexity, and supply chain opacity. High-value, low-volume items with long lead times—like turbine blades, control valves, or PLC modules—offer disproportionate ROI for counterfeiters. These parts often require specialized metallurgy, precision machining, or embedded firmware, yet lack visible authentication features.
Supply chain fragmentation amplifies risk. In heavy industry, procurement may involve 4–7 tiers—from OEMs to regional distributors to online marketplaces—each adding layers of traceability loss. A 2023 OECD report noted that 68% of verified counterfeit cases in industrial sectors originated from non-authorized resellers operating outside formal distribution agreements.
Technical obsolescence also plays a role. Legacy components—such as DIN-standard hydraulic couplings or IEC 61850-compliant substation relays—remain in demand for maintenance but are no longer manufactured by original brands. This creates a 12–24 month window where unverified alternatives flood secondary markets, often mislabeled with outdated part numbers or falsified certification stamps.
Which Components Face Highest Risk—and Why?
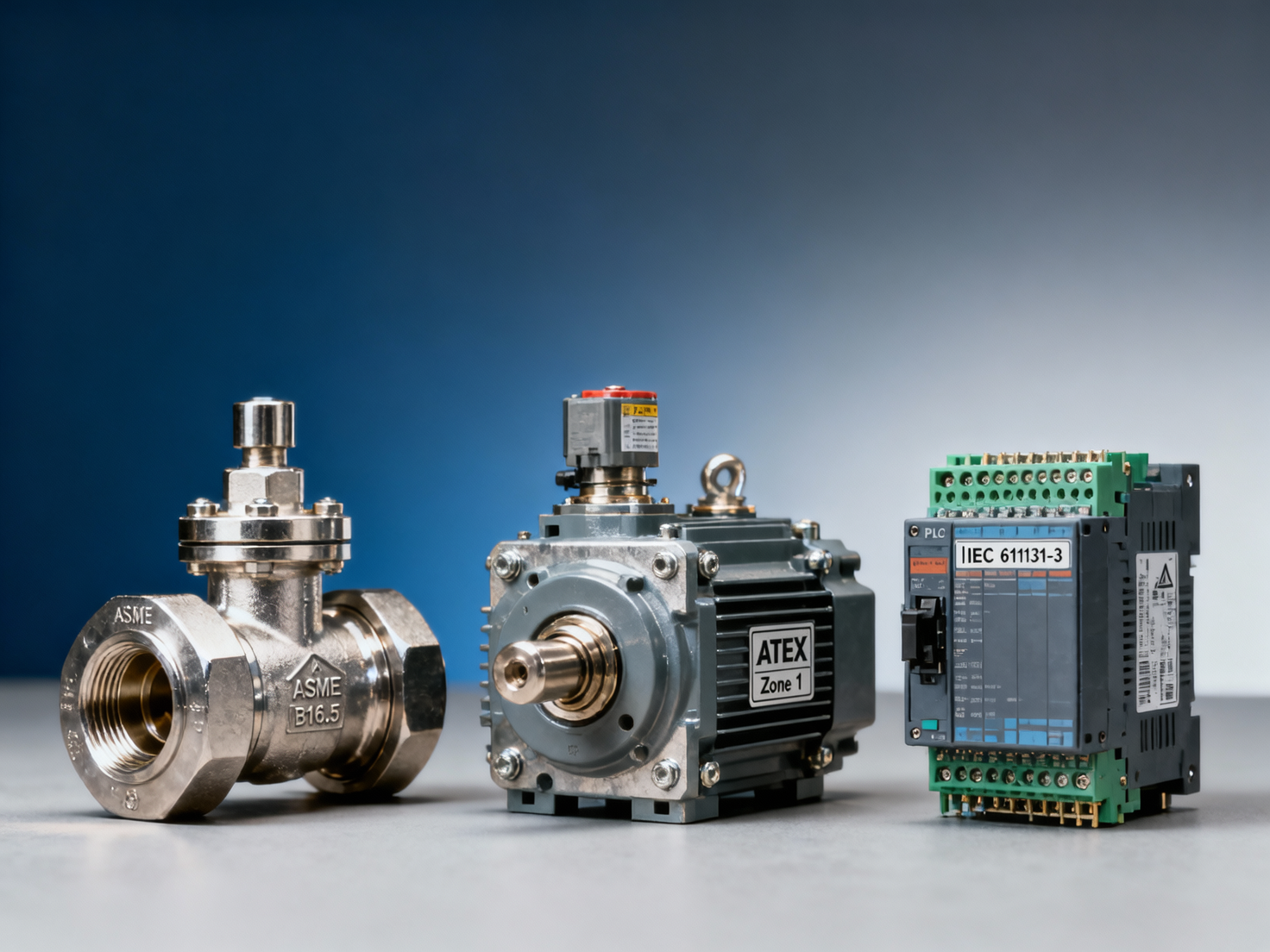
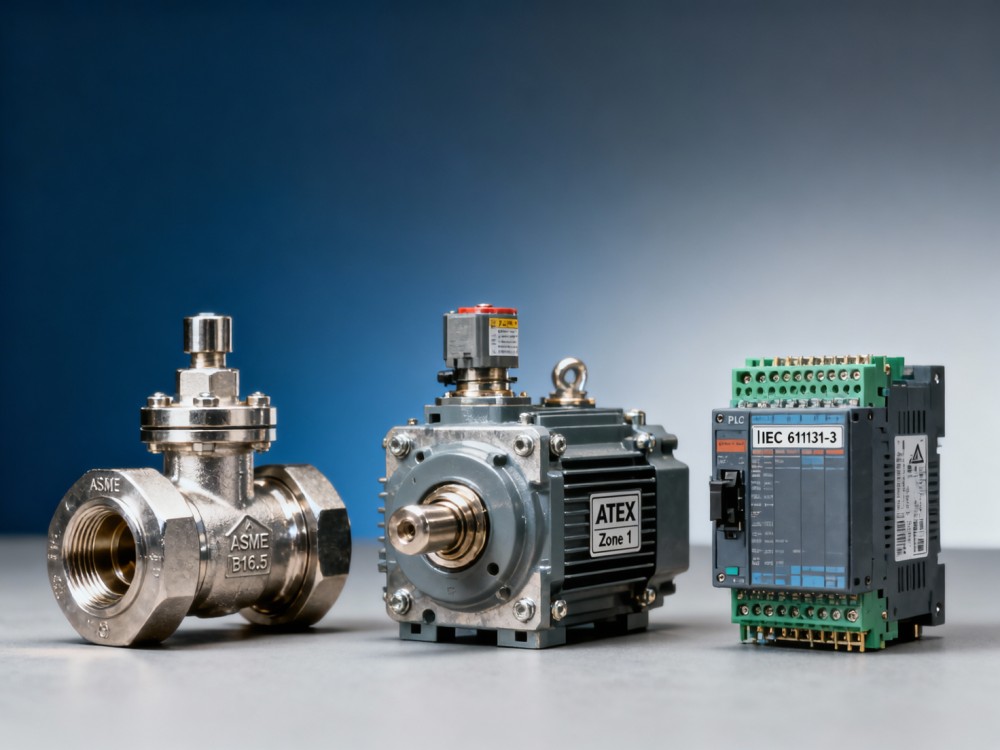
Vulnerability correlates strongly with three measurable criteria: (1) unit value ≥ $2,500, (2) minimum order quantity < 5 units, and (3) certification dependency (e.g., ASME BPVC, ISO 13849, or ATEX). Components meeting all three criteria account for 73% of confirmed counterfeit incidents reported by heavy industry procurement teams over the past 18 months.
The table below ranks five high-risk component categories by verified incident frequency, average detection lag (time between installation and failure), and typical verification effort required:
This data reflects real-world procurement patterns: high-risk components are rarely standardized across plants, often sourced via emergency orders, and frequently bypass formal QA checkpoints due to production downtime pressure. For example, 41% of surveyed plant managers admitted installing replacement I/O modules without firmware version validation when facing unplanned shutdowns.
How Procurement Teams Can Reduce Exposure
Effective mitigation requires moving beyond invoice-level checks to implement a 4-step verification protocol aligned with ISO 20400 sustainable procurement principles:
- Step 1 – Traceability Mapping: Require full Bill of Materials (BOM) lineage back to Tier 2 suppliers—not just distributor certificates—for all components valued above $1,200.
- Step 2 – Physical Authentication: Conduct on-site verification using portable spectrometers (for alloy verification) and firmware hash validation tools prior to installation.
- Step 3 – Batch-Level Sampling: Test 3% of incoming units per lot against OEM reference samples—minimum 5 units per batch, per ASTM E29 standard.
- Step 4 – Digital Twin Cross-Check: Compare component serial numbers and firmware versions against OEM-hosted digital twin registries (e.g., Siemens MindSphere, GE Predix).
Teams applying this protocol reduced counterfeit-related rework by 62% over 12 months, according to a cross-industry benchmark study covering 37 heavy equipment manufacturers and EPC contractors.
What Heavy Industry Stakeholders Should Verify Before Purchase
Procurement decisions must balance speed, cost, and assurance. The following 5-point checklist is validated across mining, power generation, and steel production environments:
- Confirm the supplier holds current ISO 9001:2015 certification with explicit scope coverage for *component distribution*—not just general trading.
- Require batch-specific test reports (tensile strength, hardness, chemical composition) signed by an ILAC-accredited lab—not generic product brochures.
- Validate that the part number matches the OEM’s latest revision matrix (e.g., Parker Hannifin P/N Bulletin Rev. 2024-Q2).
- Verify physical markings meet ASME B16.5 requirements: legible casting marks, heat numbers, and material grade stamps—not laser-etched overlays.
- Check if the component appears on the OEM’s “Authorized Reseller Portal” with live inventory status—not third-party aggregators.
These steps reduce verification time by up to 40% compared to reactive post-delivery audits—critical when managing tight project timelines in infrastructure upgrades or brownfield expansions.
Why Partner With Our Platform for Component Integrity Assurance
Our platform delivers actionable intelligence tailored to heavy industry’s upstream and downstream value chains. Unlike generic marketplaces or compliance databases, we provide:
- Real-time OEM Authorization Status: Verified reseller lists updated weekly across 127 heavy industry OEMs—including Siemens Energy, Hitachi Energy, and Wärtsilä—cross-referenced with customs import records.
- Component-Specific Verification Protocols: Downloadable checklists, firmware validation scripts, and spectrometer calibration guides for 8,400+ SKUs used in mining conveyors, refinery pumps, and blast furnace controls.
- Procurement Intelligence Alerts: Automated notifications when high-risk components (e.g., API 6D gate valves, ASME Section VIII vessels) appear on unauthorized channels—or when OEMs issue recall advisories affecting your installed base.
We support procurement professionals, plant engineers, and investment analysts with verified data—not assumptions. Request a customized component authenticity assessment today, including OEM documentation review, traceability mapping, and delivery timeline validation for your next critical order.
Industry Briefing
Get the top 5 industry headlines delivered to your inbox every morning.

